Compelling account: In 2021, 32 per cent of the organisations targeted by a cyberattack agreed to pay a ransom to the hackers, compared with 26 per cent in 2020, according to the Thales Cyberthreat Handbook 2022.
MUSCAT: Thales, a global leader in cybersecurity and data protection, has launched the latest edition of its Thales Cyberthreat Handbook 2022, which offers unprecedented insights into potential attacks being wages by all kinds of perpetrators – hackers, criminal organisations and state-sponsored forces alike. The unveiling took place at the annual Thales Media Day organised by the company recently.
According to the company, the public health crisis has created new vulnerabilities due to the increase in remote working, growing use of data networks and the digitalisation of almost every sector of the economy. Between 2020 and 2021 in Europe, this led to an unprecedented 37.7 per cent increase in the number of cyberattacks, said Thales, citing France's national information systems security agency (ANSSI).
Developing good "cyber hygiene" practices and a better knowledge and understanding of cyberattacks are the only ways to address this situation and collectively develop an effective response to cyberthreats, Thales stresses.
As part of this effort, Thales's Cyber Threat Intelligence (CTI) unit gathers, analyses, filters and correlates data on each type of attack, the hackers behind them and the techniques, tactics and procedures they use, in order to improve the ability of organisations to detect cyberattacks and fight against them.
The Thales CTI unit has just published the 2022 edition of its Thales Cyberthreat Handbook on the Internet, with details about the extent of these attacks and the ways in which hacker groups are organised.
Over the last five years, experts from Thales's CTI unit have analysed more than 20,000 attacks in nine geographic areas and 16 sectors of activity. These cyberattacks point to an impressive level of organisation within the hacker community as well as the emergence of new types of advanced persistent threats and new hybrid relationships between the public sector and private operators.
To expand their activities and boost profitability, hacker groups have gradually organised and structured their operations along the same lines as small or medium-sized businesses. Their new organisations include R&D departments to improve the effectiveness of cyberattacks and constantly develop innovative techniques and attack profiles, human resources departments to recruit new hacker profiles, and legal departments to negotiate financial arrangements with attack victims.
“Since the pandemic began, our societies have witnessed a major surge in malicious cyber activity,” comments Patrice Caine, Chairman & CEO – Thales Group. “We may not always be immediately aware of this vulnerability, but it represents a real risk to our economies, our democracies and our daily lives. The increase in cyberattacks is almost directly proportional to the speed of our digital transformation. The more connected the world becomes, the greater its surface of attack will be.”
Caine further adds: “For greater speed and efficiency, a growing number of companies are connecting their suppliers to their enterprise IT systems, potentially offering cybercriminals new ways to breach their data by finding weak links in the supply chain and gaining access to the information systems of major companies and State institutions.”
According to the 2022 Thales Cyberthreat Handbook, the increasing number of organisations that agree to pay a ransom to retrieve their data after an attack suggests that these legal departments play a crucial role in guaranteeing the lucrative nature of malicious cyber activity.
In 2021, 32 per cent of the organisations targeted by a cyberattack agreed to pay a ransom to the hackers, compared with 26 per cent in 2020. One hacker group even managed to extort 180 million euros from the victims of a single cyberattack. In their constant quest for profitability, many hackers conduct cost/benefit analyses to identify the industries and countries that are the most open to digitalisation of their business models.
The Thales Cyberthreat Handbook reveals that 72 per cent of the 20,000 attacks analysed targeted the defence sector and public administrations, and 62 per cent targeted the telecommunications sector. North America accounted for 72 per cent of the attacks, and Europe accounted for 66 per cent.
The 2022 Thales Cyberthreat Handbook also reports a rise in the number of state-sponsored attacks over the last five years, in particular linked to the growing use of "dormant" malware. In this type of attack, the hackers install a virus on the organisation's IT system to gain access to the data on its networks and can then conduct long-term espionage operations, which are more dangerous by definition.
Dormant malware can remain undetected on an organisation's systems for anything from two years to more than a decade. This kind of attack is becoming more prevalent as private enterprises work more closely with government agencies to counter cyberthreats, and as hackers become better organised and more professional. Today, more and more governments outsource their cyber activity and have become increasingly reliant on outside hacker groups.
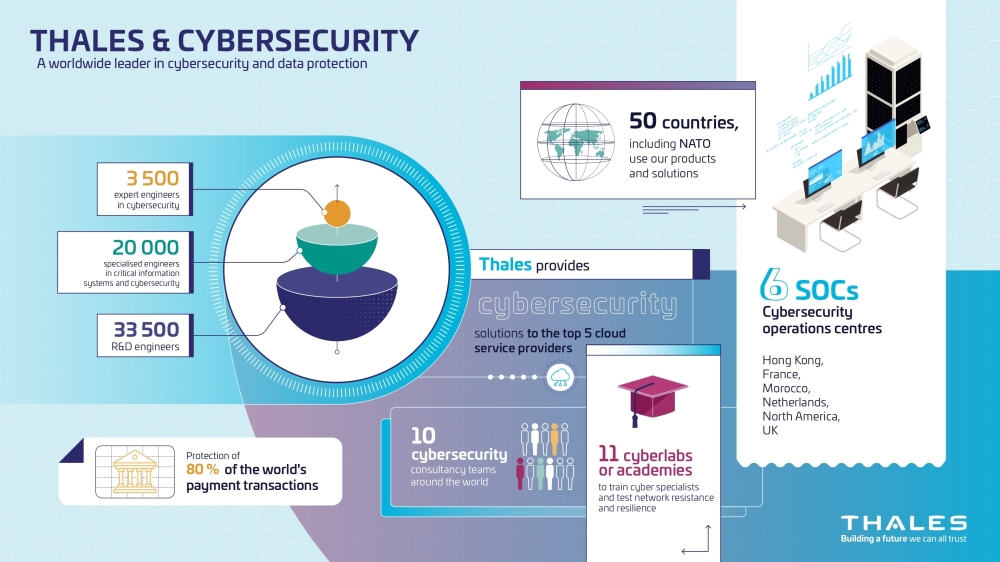
Thales serves 130 major customers worldwide, including governments, critical national infrastructure providers and public administrations. The Group provides cybersecurity for 19 of the world's 20 largest banks, nine of the 10 Internet giants, as well as thousands of businesses of all sizes.
The Thales value proposition is based on three major product families: Cybels, a complete platform of cybersecurity services including risk assessment, training and simulation, and cyberattack detection and response; Sovereign products including encryptors and sensors to protect critical information systems; and a digital platform for data protection, cloud security and access control.
Oman Observer is now on the WhatsApp channel. Click here